What cloud security steps should regulated SMBs follow in 2026?
Regulated small and mid-sized businesses must secure cloud systems with strong access controls, encryption, monitoring, and compliance-ready policies. A clear security checklist helps protect sensitive data and ensures organizations remain aligned with regulatory standards.
Why is cloud security critical for regulated businesses?
Businesses handling sensitive data—such as healthcare records, financial information, or government data—must meet strict cybersecurity requirements. Without proper cloud security controls, organizations risk data breaches, compliance violations, and operational disruption.
How can SMBs simplify cloud security compliance?
By following a structured cloud security checklist that includes identity protection, data encryption, monitoring, and employee training. When implemented correctly, these safeguards help businesses maintain strong security and regulatory readiness.
Why Cloud Security Is a Top Priority for Regulated SMBs
Cloud platforms have become the backbone of modern business operations. From file storage and collaboration platforms to accounting software and customer data systems, many critical workloads now run in the cloud.
While cloud solutions offer flexibility and scalability, they also introduce new security responsibilities.
Regulated industries—including healthcare, financial services, aerospace, and government contractors—must ensure that sensitive information remains protected in cloud environments.
Many organizations handling regulated data must follow strict cybersecurity frameworks. For example, businesses handling Controlled Unclassified Information must comply with NIST SP 800-171 security controls, which include strict requirements around access management, monitoring, and data protection.
For SMBs, maintaining compliance while managing cloud infrastructure can feel overwhelming without a clear security strategy.
A Practical 2026 Cloud Security Checklist for SMBs
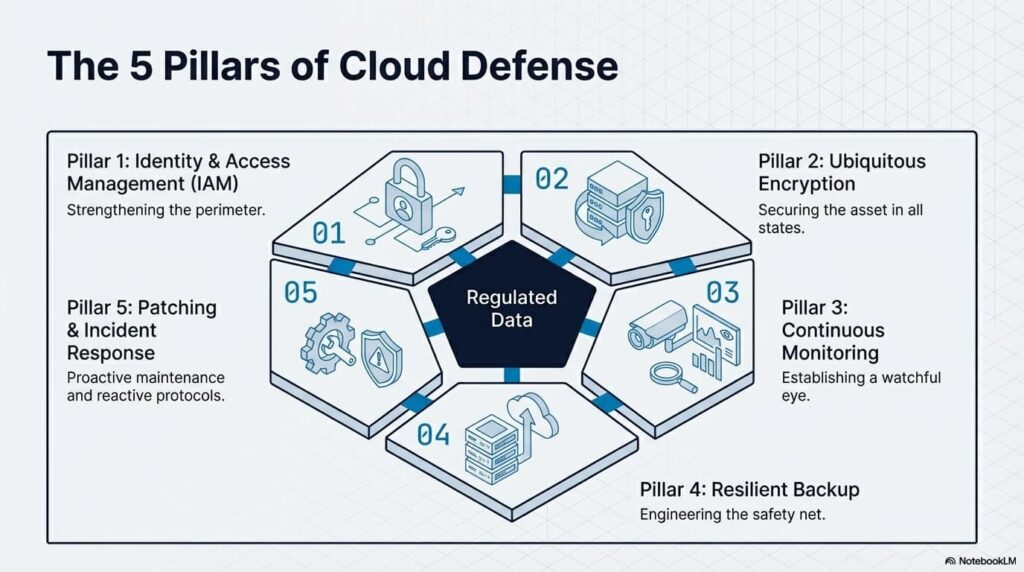
A strong cloud security posture begins with a structured set of controls designed to protect sensitive data and maintain compliance.
Below are essential steps regulated SMBs should implement when securing their cloud environments.
Strengthen Identity and Access Management
Access control is one of the most critical aspects of cloud security.
Organizations should ensure that only authorized users can access sensitive systems and data.
Best practices include:
• Enforcing multi-factor authentication for all users
• Limiting administrative privileges
• Implementing role-based access controls
• Regularly reviewing user access permissions
• Removing access immediately when employees leave the organization
These controls significantly reduce the risk of unauthorized access.
Encrypt Sensitive Data Everywhere
Encryption protects sensitive information both while it is stored and when it is transmitted between systems.
Most regulatory frameworks require encryption as a core security control.
Key encryption practices include:
• Encrypting sensitive data stored in cloud systems
• Using secure connections for data transfers
• Protecting backup files with encryption
• Managing encryption keys securely
Encryption helps ensure that even if data is intercepted or accessed improperly, it remains unreadable.
Monitor Cloud Activity Continuously
Visibility is essential for identifying suspicious behavior before it becomes a major incident.
Cloud monitoring tools help organizations detect unusual activity, failed login attempts, or unauthorized changes.
Security monitoring should include:
• Continuous system logging
• Alerts for suspicious login attempts
• Monitoring file access and downloads
• Tracking administrative actions
Regular monitoring allows organizations to respond quickly to potential threats.
Implement Secure Backup and Recovery Systems
Cloud systems still require reliable backup strategies.
Accidental deletions, ransomware attacks, or system failures can disrupt business operations if data is not recoverable.
Organizations should maintain:
• Automated cloud backups
• Secure off-site backup storage
• Regular backup testing
• Clearly documented recovery procedures
Reliable backups ensure business continuity during unexpected events.
Maintain Patch and Update Management
Outdated software remains one of the most common causes of cybersecurity vulnerabilities.
Cloud-based applications and systems must be updated regularly to protect against emerging threats.
Organizations should:
• Apply security patches promptly
• Monitor vendor updates and security advisories
• Automate patch management when possible
• Maintain documentation of system updates
Regular patching helps close security gaps before attackers can exploit them.
Develop a Cloud Incident Response Plan
Even the most secure organizations must be prepared to respond to cybersecurity incidents.
A clear incident response plan ensures teams know how to act quickly when suspicious activity occurs.
Incident response planning should include:
• Defined reporting procedures
• Clear escalation paths
• Data breach response protocols
• Communication guidelines during incidents
Organizations with documented response plans recover faster and minimize disruption.
Compliance Frameworks Driving Cloud Security Requirements
Regulated SMBs must often align with multiple cybersecurity frameworks depending on their industry.
For example, government contractors and organizations handling sensitive federal information may need to follow requirements such as:
• FAR cybersecurity controls
• NIST SP 800-171
• CMMC certification requirements
• DFARS regulations
These frameworks require strong access controls, system monitoring, encryption, and incident response planning.
For regulated SMBs, aligning cloud security practices with these frameworks is essential for maintaining contracts and regulatory standing.
Why Businesses Partner with HD Tech for Cloud Security
Many SMBs rely on experienced IT partners to manage the complexity of cloud infrastructure and security compliance.
HD Tech helps organizations secure cloud environments while ensuring systems remain reliable and easy to manage.
Based in Orange County, California and serving businesses across the United States, HD Tech supports organizations that depend on secure technology and responsive IT support.
Businesses working with HD Tech benefit from:
• Proactive cloud security monitoring
• Help desk support for cloud-based systems
• Guidance navigating complex compliance requirements
• Strong data protection strategies
• Reliable backup and recovery planning
By combining proactive IT support with strong cybersecurity practices, organizations can protect sensitive data while maintaining operational efficiency.
The Future of Cloud Security for SMBs
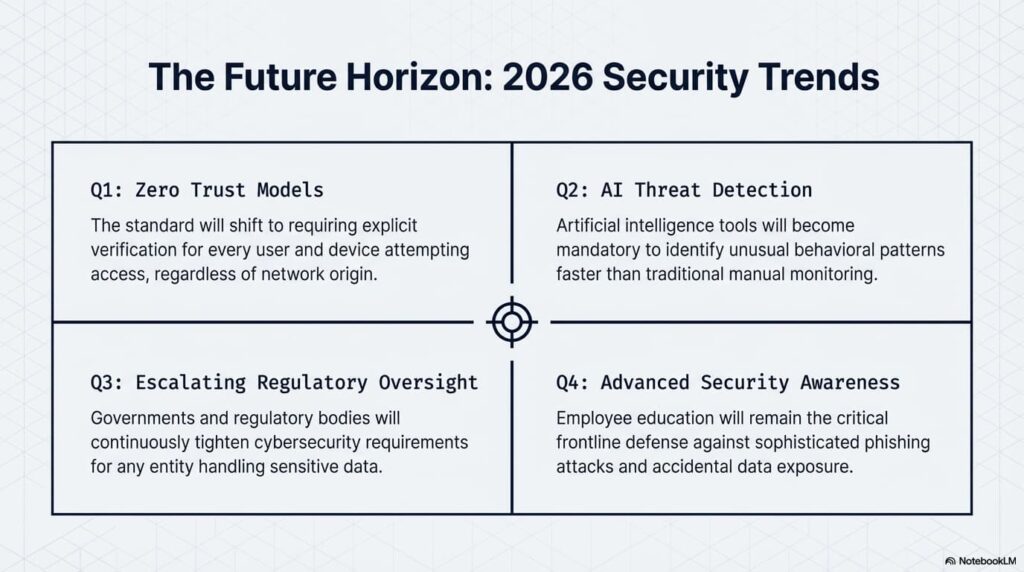
As cloud adoption continues to grow, security strategies will continue evolving.
Key trends expected in the coming years include:
Zero Trust Security Models
Organizations will increasingly require verification for every user and device attempting to access cloud systems.
Automated Threat Detection
Artificial intelligence tools will help identify unusual behavior faster than traditional monitoring systems.
Greater Regulatory Oversight
Governments and regulatory bodies will continue strengthening cybersecurity requirements for organizations handling sensitive data.
Improved Security Awareness Training
Employee education will remain a critical part of preventing phishing attacks and data exposure.
For regulated SMBs, cloud security will remain a critical part of protecting business operations and maintaining compliance.
Frequently Asked Questions About Cloud Security for SMBs
What is cloud security for small businesses?
Cloud security refers to the policies, tools, and practices used to protect data and systems hosted in cloud environments. This includes access control, encryption, monitoring, and backup strategies designed to keep sensitive information secure.
Why do regulated SMBs need stronger cloud security?
Organizations in regulated industries often store sensitive data such as financial records, healthcare information, or government-related data. Security controls help protect this information and ensure businesses remain compliant with regulatory standards.
Is cloud storage secure for regulated data?
Cloud platforms can be very secure when configured correctly. However, organizations must implement strong access controls, encryption, monitoring, and security policies to ensure sensitive information remains protected.
How often should cloud security be reviewed?
Cloud security configurations should be reviewed regularly, especially when systems change, new users are added, or regulatory requirements evolve. Periodic assessments help identify vulnerabilities and maintain compliance.
What is the biggest cloud security risk for SMBs?
One of the most common risks is misconfigured access controls, which can allow unauthorized users to access sensitive data. Proper identity management and regular access reviews help prevent this issue.
Protect Your Cloud Systems with Trusted IT Support
Cloud systems power many of today’s most important business operations. Keeping those systems secure is essential for protecting data, maintaining compliance, and ensuring business continuity.
HD Tech helps organizations implement secure cloud environments, proactive monitoring, and reliable IT support that keeps systems running smoothly.
If your business wants stronger cloud security and dependable technology support, the team at HD Tech is ready to help.
Call 877-540-1684 to speak with an IT specialist and learn how secure cloud infrastructure can support your organization’s growth.
Areas Served
HD Tech is headquartered in Orange County, California, supporting businesses across Irvine, Anaheim, Santa Ana, Huntington Beach, Newport Beach, and surrounding communities while providing IT and cybersecurity services nationwide across the United States.