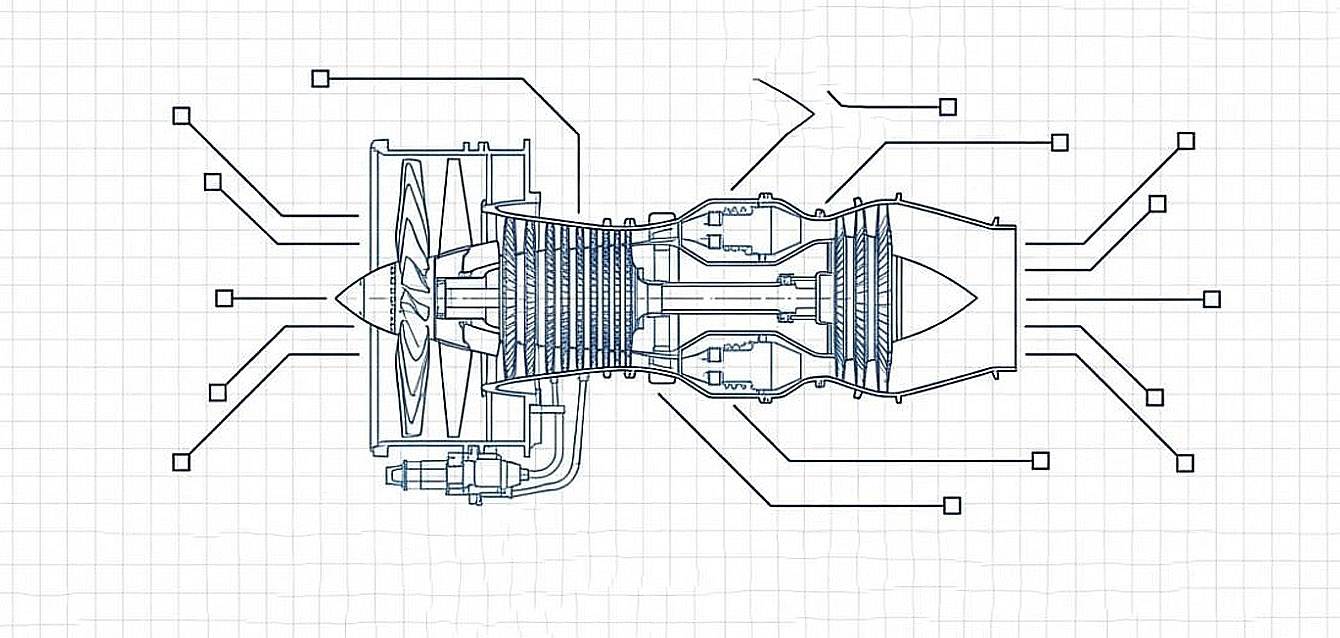
The Challenge: When Downtime Risks National Security Located in the heart of Huntington Beach’s aerospace corridor, a high-tier defense contractor was facing a dual crisis. Not only was legacy network hardware causing frequent, unpredictable downtime—stalling production lines for critical components—but they…
Secure Cloud Evolution for Costa Mesa’s Financial Leaders
The Challenge: Balancing Productivity with Stringent Compliance A growing accounting firm in Costa Mesa, known for its participation in Orange County’s premier financial networking circles, faced a common professional services hurdle. Their on-premises server infrastructure was struggling to support a modern,…
Elevate Security with 24×7 Email Monitoring
Exploring the Tangible Benefits of Real-Time Oversight for Email Threats in Modern Organizations In a digital world where email remains the primary communication channel for organizations, the risk of business email compromise (BEC) has never been higher. Attackers continually evolve their…
Strengthen Your Organization with Cybersecurity Training
Exploring the Tangible Benefits of Continuous Cyber Awareness Training for Modern Organizations In today’s digital landscape, where cyber threats are as likely to come from human error as from sophisticated malware, organizations must recognize that their first and last line of…
Elevate Cyber Defense with SOC Monitoring
Exploring the Tangible Benefits of Real-Time Security Oversight for Modern Organizations In an era where cyber threats evolve faster than ever, businesses can no longer rely on passive security measures. The need for proactive, vigilant security operations has never been greater….
Continuous Vulnerability Scanning for Enterprise Security
Unlocking the Power of Proactive Vulnerability Management for Modern Organizations In a digital landscape where every endpoint and application presents a potential doorway for attackers, waiting for a breach is no longer an option. Today’s organizations require relentless vigilance, especially when…